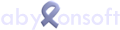
Tray-Icons are small buttons, which are displayed in the taskbar at the bottom right, next to the clock.
These icons are used to display information and call functions. In the preferences, Windows deactivates tray icons of programs so that they are not displayed for the time being. The following section describes how the settings for all or individual icons can be set.
NOTE The description is general. Depending on the program, you must select the appropriate tray icon. You can find this in the help or the FAQ's.
How do I open the settings for the tray icons?
To the left of the clock, there is a small white arrow pointing upwards, which can be used to display the other tray icons.
With "Customize" you can define the behavior of the tray icons. The "Info Area Symbols" window opens.
NOTE Below are alternative ways to open this window.

In the settings window for info area symbols, you can define the behavior of each individual tray icon.
Select the corresponding icon and select "Show icon and notifications" as option. After that you will find the tray icon on the taskbar to the left of the clock at any time.
Alternatively, you can enable the option "Always show all icons and notifications on the taskbar". In this case, the tray icons of future programs will also be displayed directly on the taskbar.
Alternative 2 to open the notification area icon settings
Move the mouse to a free area of the taskbar and press the right mouse button. Select Properties from the menu. The dialog for customizing the info area symbols opens on the Taskbar page via the "Customize" button.

Alternative 3 to open the notification area icon settings
As a further option, you can also open the Control Panel via the Start menu. Select "Large Icons" or "Small Icons" in the upper right corner. Now you can open the settings via the "Info Area Symbols" icon.